Axios NPM Package Compromise: A Deep Dive into the Supply Chain Attack

Axios NPM Package Compromise: A Deep Dive into the Supply Chain Attack
The recent compromise of the Axios npm package has sent shockwaves through the software development community. This supply chain attack, attributed to a North Korea-nexus threat actor, highlights the vulnerabilities in our software ecosystems. According to recent reports, the Axios breach is a serious threat to software security, necessitating immediate action to minimize the blast radius.
Understanding the Axios NPM Package
Axios is a widely used JavaScript library for making HTTP requests from browsers and Node.js. Its popularity makes it a prime target for malicious actors seeking to exploit the software supply chain. The recent compromise involved a threat actor publishing a malicious version of the Axios package to the npm registry.
The Attack Vector
The attack on the Axios package was meticulously planned and executed. The threat actor first published a clean version of the package to establish credibility. After waiting for 18 hours, they updated the package with malicious code. This delay allowed the package to bypass many security tools that flag suspicious activity from zero-history accounts.
Steps of the Attack
- Initial Publication: The attacker published a clean version of the Axios package.
- Waiting Period: The package remained clean for 18 hours to establish trust.
- Malicious Update: The package was updated with malicious code.
- Exploitation: Users who downloaded the updated package were compromised.
Impact of the Compromise
The compromise of the Axios package has far-reaching implications. Given its widespread use, the malicious package could potentially affect thousands of applications and systems. The impact includes data breaches, system compromises, and potential further propagation of the malware.
The Axios compromise is a wake-up call for the software development community. It highlights the need for robust security measures and continuous monitoring.
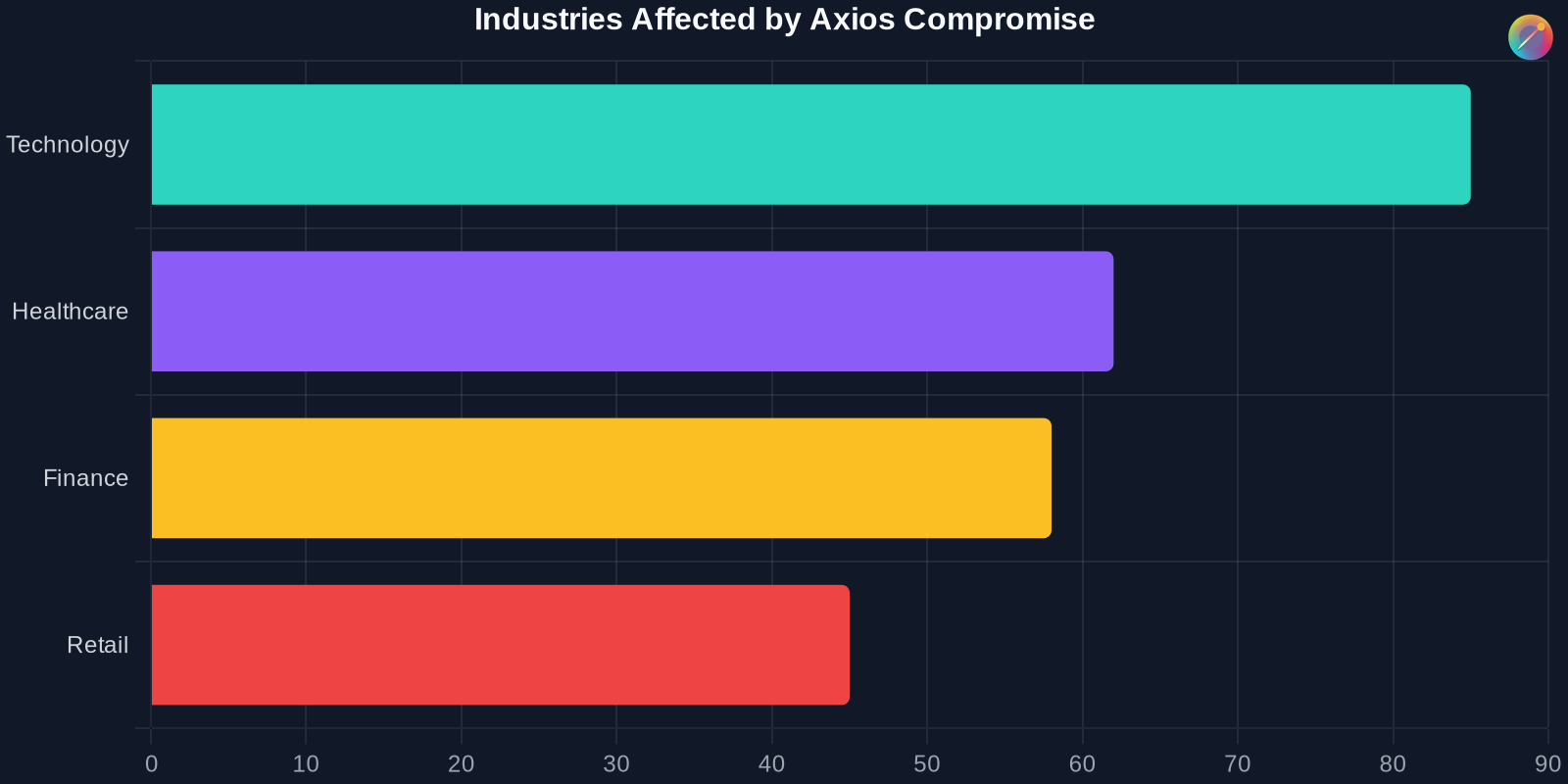
Industries Affected
The Axios package is used across various industries, each facing unique risks and challenges due to the compromise.
Response and Mitigation
In response to the Axios compromise, several steps have been taken to mitigate the impact and prevent future incidents. These include:
- Removal of Malicious Package: The compromised package was removed from the npm registry.
- Security Advisories: Security advisories were issued to alert users of the compromise.
- Updates and Patches: Developers were advised to update to a secure version of the package.
- Enhanced Security Measures: Additional security measures were implemented to prevent similar incidents.
Lessons Learned
The Axios compromise offers several key lessons for the software development community:
- Vigilance: Continuous monitoring and vigilance are essential for detecting and responding to security threats.
- Trust but Verify: Even widely trusted packages can be compromised. Always verify the integrity of dependencies.
- Incident Response: Having a robust incident response plan can minimize the impact of security breaches.
Future Implications
The Axios compromise has significant implications for the future of software security. It highlights the need for:
- Enhanced Security Tools: Improved tools for detecting and preventing supply chain attacks.
- Collaboration: Greater collaboration among developers, security researchers, and platform providers.
- Education: Increased awareness and education about software security best practices.
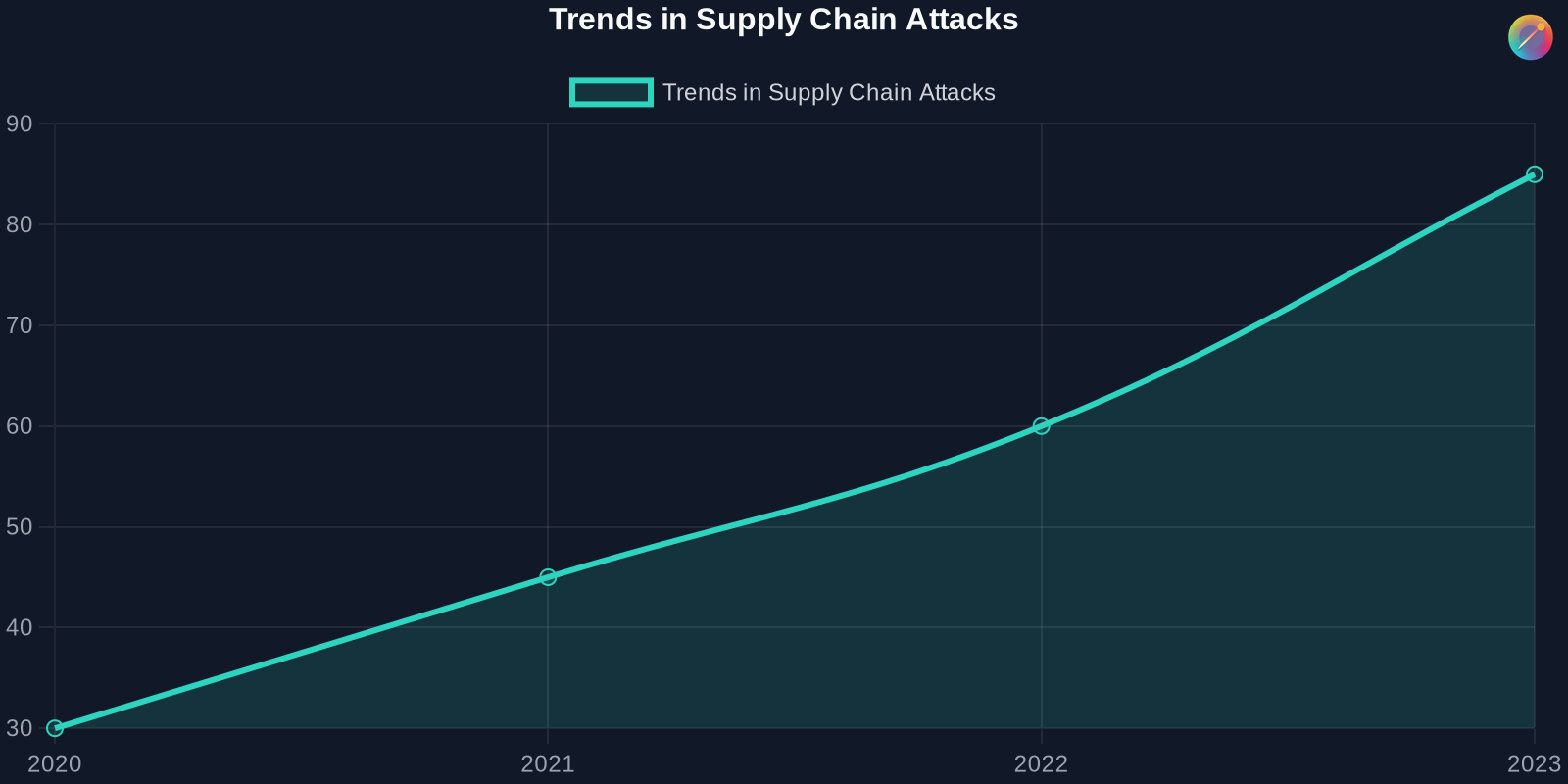
Trends in Supply Chain Attacks
Supply chain attacks have been on the rise, with increasing sophistication and impact.
Conclusion
The compromise of the Axios npm package is a stark reminder of the vulnerabilities in our software supply chains. It underscores the need for continuous vigilance, robust security measures, and proactive incident response. By learning from this incident and implementing best practices, we can better protect our systems and data from future threats.